Ledger Login — Complete Security Guide to Safe Self-Custody, Hardware Authentication & Crypto Protection
Learn how to log into Ledger safely, understand the hardware architecture behind the security, recognize phishing attempts, and manage your crypto assets with confidence using cold storage principles and offline signing.
Why Ledger Login Is a Security-Critical Step
Ledger devices are designed around a simple philosophy: your private keys should never touch the internet.
But while hardware wallets protect keys offline, attackers target the human element — using deceptive links, cloned websites, and fake login portals.
Proper ledger login involves a combination of software interface and device-side authentication, which separates viewing from signing.
Understanding this flow strengthens your protection and helps you avoid scams involving private keys, recovery phrases, transaction signatures, cold storage, and blockchain verification.
This guide breaks down the entire process in a beginner-friendly way while keeping the technical concepts clear and accessible.
But while hardware wallets protect keys offline, attackers target the human element — using deceptive links, cloned websites, and fake login portals.
Proper ledger login involves a combination of software interface and device-side authentication, which separates viewing from signing.
Understanding this flow strengthens your protection and helps you avoid scams involving private keys, recovery phrases, transaction signatures, cold storage, and blockchain verification.
This guide breaks down the entire process in a beginner-friendly way while keeping the technical concepts clear and accessible.
What Actually Happens During Ledger Login?
When you log into Ledger:
This separation creates a secure boundary between the interface and the signing environment, which is why Ledger remains resistant to malware, remote attacks, and keylogging attempts.
- Ledger Live offers a visual dashboard
- Your hardware wallet stores private keys offline
- Authentication happens on the physical device
- Transactions are signed internally
This separation creates a secure boundary between the interface and the signing environment, which is why Ledger remains resistant to malware, remote attacks, and keylogging attempts.
A Warning Story: The Fake Ledger Login Page
Ethan typed “Ledger login” into a search engine and clicked a page that looked official.
The site asked him to “verify backup words,” a request that immediately raised a red flag.
Ledger devices never request recovery phrases online — the phrase stays offline and is never typed into any digital interface.
Ethan closed the site and checked the official domain before proceeding safely.
**Scammers rely on urgency and imitated design. Awareness stops them before they even begin.**
The site asked him to “verify backup words,” a request that immediately raised a red flag.
Ledger devices never request recovery phrases online — the phrase stays offline and is never typed into any digital interface.
Ethan closed the site and checked the official domain before proceeding safely.
**Scammers rely on urgency and imitated design. Awareness stops them before they even begin.**
Ledger Login — Safe Workflow
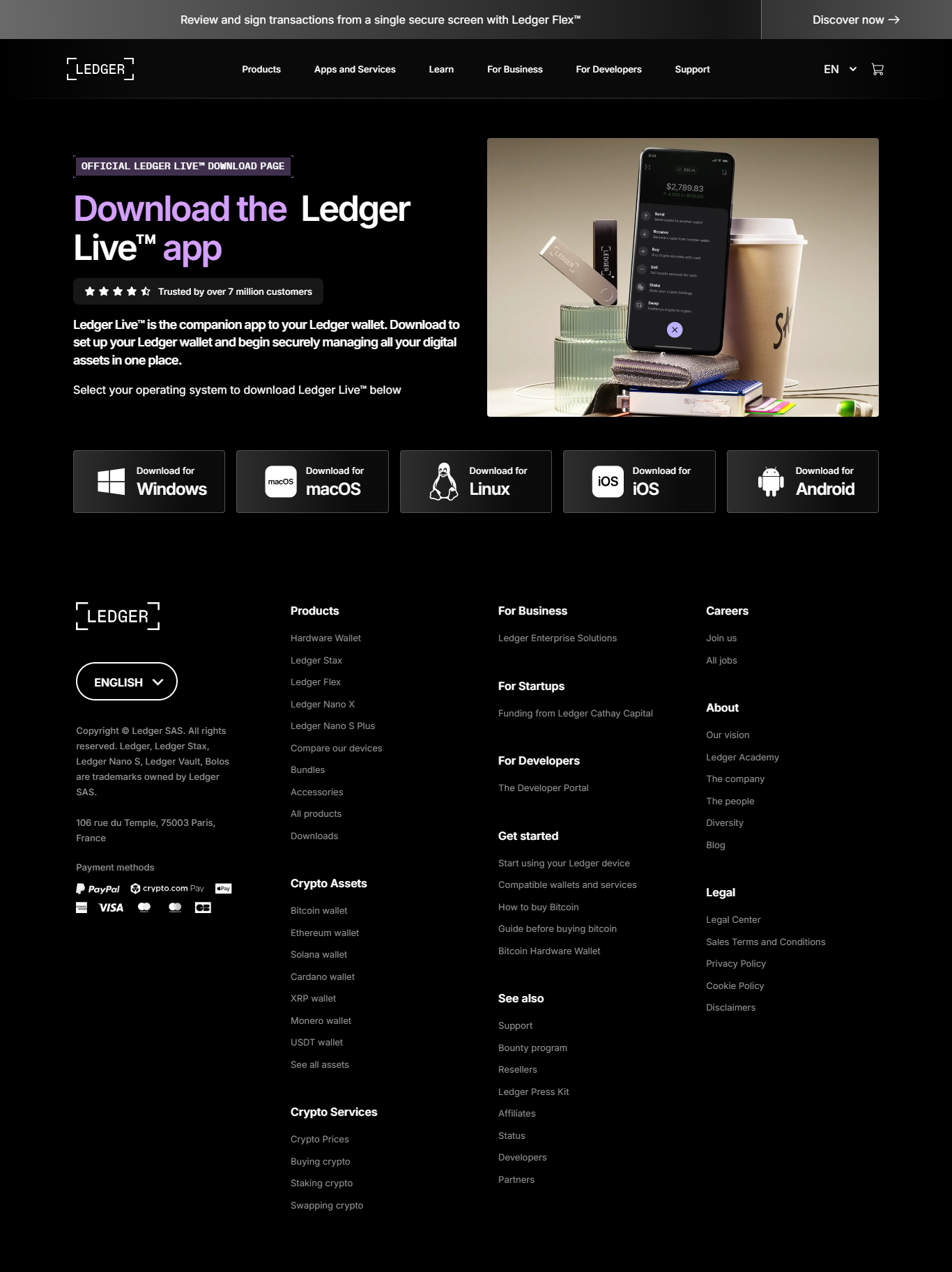
1. Download Ledger Live Only From the Official Site
Fraudulent clones often appear as top search results.
2. Install and Open Ledger Live
The app serves as a viewer, not a signer.
3. Connect Your Ledger Device
USB or Bluetooth depending on your model.
4. Enter PIN Directly On the Hardware Wallet
PIN never reaches your computer — authentication remains offline.
How Ledger Protects Private Keys
Ledger devices combine multiple defenses:
Technologies such as public-key cryptography and deterministic wallets support this architecture, creating a resilient environment for your assets.
- Secure element chips resistant to tampering
- Offline cryptographic signing
- Physical screen verification
- Cold storage isolation
Technologies such as public-key cryptography and deterministic wallets support this architecture, creating a resilient environment for your assets.
Wallet Security Comparison
| Wallet Type | Security Level | Key Control | Recommended Use |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Cold storage |
| Mobile Wallet | Medium | User | Daily spending |
| Exchange Wallet | Low | Exchange | Trading |
Essential Ledger Security Rules
✔ Only use official Ledger Live software
✔ Never type your recovery phrase online
✔ Keep physical backups offline
✔ Verify transactions on the device
✔ Beware of cloned support pages
✔ Keep your firmware updated
✔ Never type your recovery phrase online
✔ Keep physical backups offline
✔ Verify transactions on the device
✔ Beware of cloned support pages
✔ Keep your firmware updated
Frequently Asked Questions
1. Does Ledger Live store private keys?
No — keys remain inside the hardware wallet.
2. Is a password required?
Only the PIN, entered on the device.
3. Can Ledger be hacked?
Not in a way that exposes keys, due to offline signing.
4. Does it support many cryptocurrencies?
Yes — thousands.
5. What if I lose my hardware wallet?
Restore your accounts using the recovery phrase.
No — keys remain inside the hardware wallet.
2. Is a password required?
Only the PIN, entered on the device.
3. Can Ledger be hacked?
Not in a way that exposes keys, due to offline signing.
4. Does it support many cryptocurrencies?
Yes — thousands.
5. What if I lose my hardware wallet?
Restore your accounts using the recovery phrase.
Conclusion — Safe Ledger Login Protects Your Digital Wealth
Ledger login is a combination of software viewing and hardware authentication — a design that keeps your keys offline and out of reach.
By following the correct process, avoiding fake portals, and trusting the physical device over any online prompt, you build a secure self-custody environment.
Ledger’s architecture — secure elements, cold storage, physical verification, and offline signing — creates a robust foundation, but users must follow safe habits to fully benefit from it.
Choose authenticity, follow the official path, and keep your assets under your control — always.
By following the correct process, avoiding fake portals, and trusting the physical device over any online prompt, you build a secure self-custody environment.
Ledger’s architecture — secure elements, cold storage, physical verification, and offline signing — creates a robust foundation, but users must follow safe habits to fully benefit from it.
Choose authenticity, follow the official path, and keep your assets under your control — always.